Overview: Unveiling Cybersecurity Challenges in India’s Government Systems
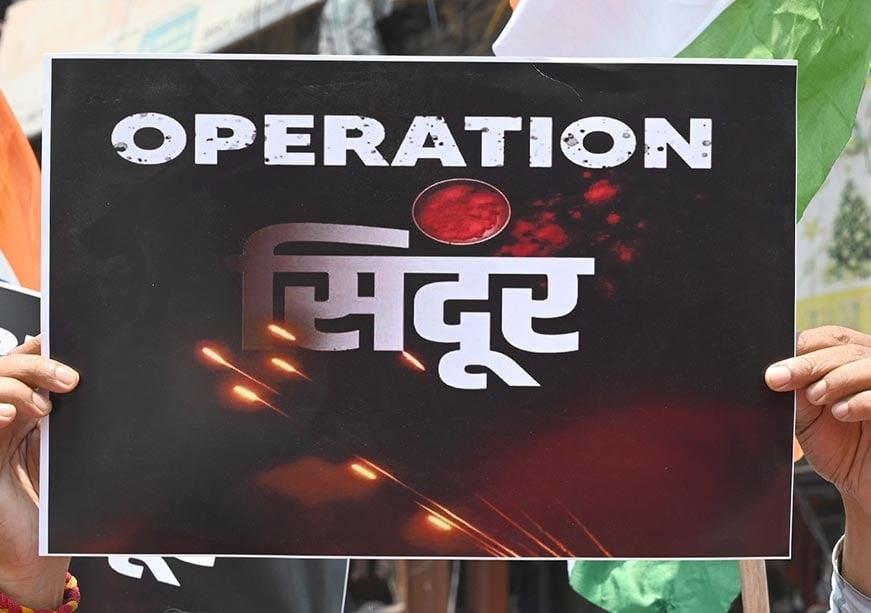
A recent investigation, dubbed “Operation Sindoor,” has brought to light a concerning reality: nearly 75% of cyber intrusions in India are aimed at government digital networks. This collaborative study, conducted by cybersecurity specialists alongside governmental bodies, reveals the escalating complexity and frequency of cyber threats confronting the nation. As public services increasingly migrate online, these findings emphasize critical weaknesses within government IT frameworks. This article explores the key insights from Operation Sindoor, assessing their implications for national security and public service continuity while stressing the urgent need for comprehensive cybersecurity enhancements.
Government Digital Infrastructure Under Siege: Key Vulnerabilities Revealed
Operation Sindoor exposes significant frailties within India’s governmental digital architecture, with three-quarters of cyberattacks targeting state-operated platforms. The report identifies several core issues that render these systems susceptible to exploitation:
- Legacy Software Usage: Numerous government applications continue to operate on outdated software versions lacking essential security patches.
- Insufficient Workforce Cyber Awareness: Many employees have not received adequate training to detect or respond effectively to evolving cyber threats.
- Inadequate Network Defenses: Weaknesses in firewall configurations create exploitable entry points for attackers.
These vulnerabilities collectively elevate risk levels and demand immediate attention through modernization efforts and capacity building.
| Vulnerability Type |
Severity Level |
| Outdated Software Platforms |
Critical |
| Lack of Employee Training |
Moderate |
| Poor Firewall Implementation |
Critical |
Understanding Cyberattack Strategies Targeting Government Networks
The analysis highlights that sophisticated threat actors employ a variety of tactics designed specifically to breach government defenses. Approximately 75% of attacks focus on exploiting both technological flaws and human vulnerabilities within official channels.
Common attack vectors identified include:
- Spear Phishing: Tailored deceptive communications aimed at tricking officials into divulging confidential credentials or clicking malicious links.
- Malfare Ransomware Attacks: Deployment of encryption malware that locks critical data until ransom demands are met.
- Dangerous SQL Injection Exploits: Manipulation techniques targeting backend databases to extract or alter sensitive information unlawfully.
- DDoS (Distributed Denial-of-Service) Assaults: Overwhelming network traffic floods designed to incapacitate essential online services temporarily.
To contextualize these threats further, below is a breakdown illustrating their prevalence alongside potential consequences for governmental operations:
| Categorized Attack Type |
% Occurrence |
Main Consequence |
| Spear Phishing
| 32% |
Unauthorized Data Access
|
| Malfare Ransomware
| 28% |
Operational Disruption
|
| Dangerous SQL Injection
| 18% |
Data Integrity Compromise
|
| DDoS Attacks
| 22%%
Operational Downtime
Strategic Measures to Enhance Cybersecurity Resilience in Public Sector Systems
Given that three out of every four cyber incidents target public sector infrastructure as revealed by Operation Sindoor, it is imperative for authorities to adopt a multi-layered defense strategy combining technology upgrades with human capital development.
Key recommendations include:
- The Integration of AI-Powered Security Tools: Deploy intelligent threat detection systems capable of real-time anomaly identification and automated response mechanisms.
Routine Security Evaluations :Implement scheduled penetration testing and vulnerability assessments to identify emerging risks promptly.< / li >
< li >< b >Comprehensive Staff Education Programs : b >Mandate continuous cybersecurity awareness training focusing on recognizing phishing attempts, safe data handling practices ,< /a> & incident reporting protocols .< /a > li >
< li >< b >Public–Private Partnerships : Collaborate closely with leading technology firms specializing in cybersecurity solutions to enhance defensive capabilities.< / li >
< / ul >
Establishing dedicated incident response teams equipped with clear operational guidelines will be crucial for minimizing damage during breaches. These teams should be supported by effective communication channels ensuring swift coordination across departments.
Additionally, promoting nationwide awareness campaigns focused on best practices in digital hygiene can empower citizens as active participants in safeguarding national cyberspace integrity.
| Incident Response Element th >
| Description th >
tr >
thead >
|
| < strong >Preparation strong > td >
| Formulate detailed action plans and allocate resources ahead of potential attacks. td >
tr >
< tr >
< td >< strong >Detection strong > td >
< td >Leverage advanced monitoring tools capable detecting suspicious activities early. td >
< / tr >
< tr >
< td >< strong >Containment strong > td >
< td >/Isolate compromised systems swiftly preventing spread. td >
< / tr >
< tr >
< td >< strong >Eradication \
An In-depth Look at Cyber Threats Facing Indian Government Digital Systems
Recent findings from “Operation Sindoor,” an extensive investigation led by cybersecurity professionals collaborating with Indian government agencies, reveal an unsettling trend: approximately 75%of all cyberattacks are directed against governmental digital assets. As more administrative functions shift online—accelerated by initiatives like Digital India—the exposure risk grows exponentially. This article unpacks Operation Sindoor’s revelations about systemic weaknesses threatening national security and public service delivery while outlining strategic responses necessary amid this dynamic threat environment.
Exposing Critical Flaws Within Government IT Ecosystems
The report highlights glaring deficiencies undermining India’s state-run digital platforms’ resilience against hostile incursions:
Reliance on Obsolete Software: A significant portion operates using legacy applications lacking current security updates—creating exploitable loopholes.
- Deficient Employee Preparedness: Many civil servants lack sufficient training programs tailored toward identifying sophisticated social engineering tactics.
Suboptimal Network Defenses: Firewalls often suffer from misconfigurations or outdated rulesets failing against modern intrusion methods.
Such shortcomings amplify susceptibility levels considerably—necessitating urgent modernization paired with workforce empowerment initiatives.
“>
| >Vulnerability Category | >
>Risk Severity | >
/tr
/head
/tr
/tr
/tr
/tr
/tr
Outdated Software Platforms | Severe
Inadequate Staff Training | Moderate
Firewall Weaknesses | Severe*
/tbody
/table
>Decoding Predominant Attack Techniques Against Public Sector Networks
Cyber adversaries employ diverse strategies blending technical exploits with psychological manipulation aimed squarely at compromising sensitive governmental data repositories:
Targeted Spear Phishing Emails: Customized fraudulent messages crafted specifically toward officials intended to harvest login credentials.
- Ransomware Campaigns: Malicious code encrypts vital datasets demanding extortion payments before restoration.
SQL Injection Exploits: Intruders manipulate database queries enabling unauthorized access or alteration.
- Distributed Denial-of-Service (DDoS) Offensives: Flood attacks overwhelm servers causing temporary shutdowns disrupting citizen-facing services.
Below is an overview quantifying attack frequencies alongside their operational impacts based on recent intelligence gathered during Operation Sindoor:
” cellpadding=”10″ cellspacing=”0″ border=”1″ width=”100%” align=”center”>
>
>
| >Attack Vector | >
>Incidence Rate (%) | >
>Primary Impact th >
< / tr >
/>
/>
Table continues below:
| Attack Type | Frequency (%) | Potential Consequence |
|———————-|—————|———————-|
| Spear Phishing | 32 | Unauthorized Data Access |
| Ransomware | 28 | Service Interruptions |
| SQL Injection | 18 | Data Corruption & Theft |
| DDoS | 22 | Temporary Service Outages |
>Building a Resilient Defense Framework For Government IT Assets
To counteract this alarming trend where most assaults target public sector networks, it is vital that policymakers implement layered defense mechanisms combining cutting-edge technologies along with continuous personnel development.
Recommended actions encompass:
=””>
- =””>Adoption Of AI-Based Threat Detection Solutions : ,and incident escalation protocols.
</l i >
The establishment
of specialized incident response units equipped
with clear-cut operational guidelines will be pivotal
in mitigating damage swiftly when breaches occur.
These teams must maintain robust communication lines facilitating rapid cross-departmental coordination.
Furthermore,
nationwide educational campaigns promoting fundamental principles
of personal cybersecurity hygiene can mobilize citizens as proactive defenders
within the broader ecosystem safeguarding national cyberspace integrity.
tr>
th scope =”col”>Response Phase/th>/tr>/thead>/tbody/>
tr/>
td scope =”row”>/t d/
td>Create detailed contingency plans allocating necessary resources prior attack scenarios./t d/
tr/>
tr/>
td scope =”row”>/t d/
tdUtilize advanced monitoring solutions enabling early identification suspicious activities./t d/
tr/>
tr/>
td scope =”row”>/t d/
tdSwift isolation affected components preventing lateral movement attackers./t d/
tr/>
tr/>
td scope =”row”>/t d/
tdComplete removal malware traces restoring system integrity./ t d/
t r />
t r />
td scope =”row”>/ t d />
tdSystem restoration followed by rigorous validation before resuming normal operations./ t d />
t r />
//tbody>//table//div//section//article//html
| | |